- Step 1. Manually replicate secret GitLab values
- Step 2. Manually replicate the primary site’s SSH host keys
- Step 3. Add the secondary site
- Step 4. (Optional) Using custom certificates
- Step 5. Enable Git access over HTTP/HTTPS and SSH
- Step 6. Verify proper functioning of the secondary site
- Troubleshooting
Configure a new secondary site
The basic steps of configuring a secondary site are to:
- Replicate required configurations between the primary and the secondary site.
- Configure a tracking database on each secondary site.
- Start GitLab on each secondary site.
This document focuses on the first item. You are encouraged to first read through all the steps before executing them in your testing/production environment.
Prerequisites for both primary and secondary sites:
Step 1. Manually replicate secret GitLab values
GitLab stores a number of secret values in the /etc/gitlab/gitlab-secrets.json
file which must be the same on all of a site’s nodes. Until there is
a means of automatically replicating these between sites (see issue #3789),
they must be manually replicated to all nodes of the secondary site.
-
SSH into a Rails node on your primary site, and execute the command below:
sudo cat /etc/gitlab/gitlab-secrets.jsonThis displays the secrets that need to be replicated, in JSON format.
-
SSH into each node on your secondary Geo site and login as the
rootuser:sudo -i -
Make a backup of any existing secrets:
mv /etc/gitlab/gitlab-secrets.json /etc/gitlab/gitlab-secrets.json.`date +%F` -
Copy
/etc/gitlab/gitlab-secrets.jsonfrom the Rails node on your primary site to each node on your secondary site, or copy-and-paste the file contents between nodes:sudo editor /etc/gitlab/gitlab-secrets.json # paste the output of the `cat` command you ran on the primary # save and exit -
Ensure the file permissions are correct:
chown root:root /etc/gitlab/gitlab-secrets.json chmod 0600 /etc/gitlab/gitlab-secrets.json -
Reconfigure each Rails, Sidekiq and Gitaly nodes on your secondary site for the change to take effect:
gitlab-ctl reconfigure gitlab-ctl restart
Step 2. Manually replicate the primary site’s SSH host keys
GitLab integrates with the system-installed SSH daemon, designating a user
(typically named git) through which all access requests are handled.
In a Disaster Recovery situation, GitLab system administrators promote a secondary site to the primary site. DNS records for the primary domain should also be updated to point to the new primary site (previously a secondary site). Doing so avoids the need to update Git remotes and API URLs.
This causes all SSH requests to the newly promoted primary site to fail due to SSH host key mismatch. To prevent this, the primary SSH host keys must be manually replicated to the secondary site.
The SSH host key path depends on the used software:
- If you use OpenSSH, the path is
/etc/ssh. - If you use
gitlab-sshd, the path is/var/opt/gitlab/gitlab-sshd.
In the following steps, replace <ssh_host_key_path> with the one you’re using:
-
SSH into each Rails node on your secondary site and sign in as the
rootuser:sudo -i -
Make a backup of any existing SSH host keys:
find <ssh_host_key_path> -iname 'ssh_host_*' -exec cp {} {}.backup.`date +%F` \; -
Copy the SSH host keys from the primary site:
If you can access one of the nodes on your primary site serving SSH traffic (usually, the main GitLab Rails application nodes) using the root user:
# Run this from the secondary site, change `<primary_site_fqdn>` for the IP or FQDN of the server scp root@<primary_node_fqdn>:<ssh_host_key_path>/ssh_host_*_key* <ssh_host_key_path>If you only have access through a user with
sudoprivileges:# Run this from the node on your primary site: sudo tar --transform 's/.*\///g' -zcvf ~/geo-host-key.tar.gz <ssh_host_key_path>/ssh_host_*_key* # Run this on each node on your secondary site: scp <user_with_sudo>@<primary_site_fqdn>:geo-host-key.tar.gz . tar zxvf ~/geo-host-key.tar.gz -C <ssh_host_key_path> -
On each Rails node on your secondary site, ensure the file permissions are correct:
chown root:root <ssh_host_key_path>/ssh_host_*_key* chmod 0600 <ssh_host_key_path>/ssh_host_*_key -
To verify key fingerprint matches, execute the following command on both primary and secondary nodes on each site:
for file in <ssh_host_key_path>/ssh_host_*_key; do ssh-keygen -lf $file; doneYou should get an output similar to this one and they should be identical on both nodes:
1024 SHA256:FEZX2jQa2bcsd/fn/uxBzxhKdx4Imc4raXrHwsbtP0M root@serverhostname (DSA) 256 SHA256:uw98R35Uf+fYEQ/UnJD9Br4NXUFPv7JAUln5uHlgSeY root@serverhostname (ECDSA) 256 SHA256:sqOUWcraZQKd89y/QQv/iynPTOGQxcOTIXU/LsoPmnM root@serverhostname (ED25519) 2048 SHA256:qwa+rgir2Oy86QI+PZi/QVR+MSmrdrpsuH7YyKknC+s root@serverhostname (RSA) -
Verify that you have the correct public keys for the existing private keys:
# This will print the fingerprint for private keys: for file in <ssh_host_key_path>/ssh_host_*_key; do ssh-keygen -lf $file; done # This will print the fingerprint for public keys: for file in <ssh_host_key_path>/ssh_host_*_key.pub; do ssh-keygen -lf $file; doneThe output for private keys and public keys command should generate the same fingerprint. -
Restart either
sshdfor OpenSSH or thegitlab-sshdservice on each Rails node on your secondary site:-
For OpenSSH:
# Debian or Ubuntu installations sudo service ssh reload # CentOS installations sudo service sshd reload -
For
gitlab-sshd:sudo gitlab-ctl restart gitlab-sshd
-
-
Verify SSH is still functional.
SSH into your GitLab secondary server in a new terminal. If you are unable to connect, verify the permissions are correct according to the previous steps.
Step 3. Add the secondary site
-
SSH into each Rails and Sidekiq node on your secondary site and login as root:
sudo -i -
Edit
/etc/gitlab/gitlab.rband add a unique name for your site. You need this in the next steps:## ## The unique identifier for the Geo site. See ## https://docs.gitlab.com/ee/administration/geo_sites.html#common-settings ## gitlab_rails['geo_node_name'] = '<site_name_here>' -
Reconfigure each Rails and Sidekiq node on your secondary site for the change to take effect:
gitlab-ctl reconfigure - Go to the primary node GitLab instance:
- On the left sidebar, at the bottom, select Admin.
- On the left sidebar, select Geo > Sites.
- Select Add site.
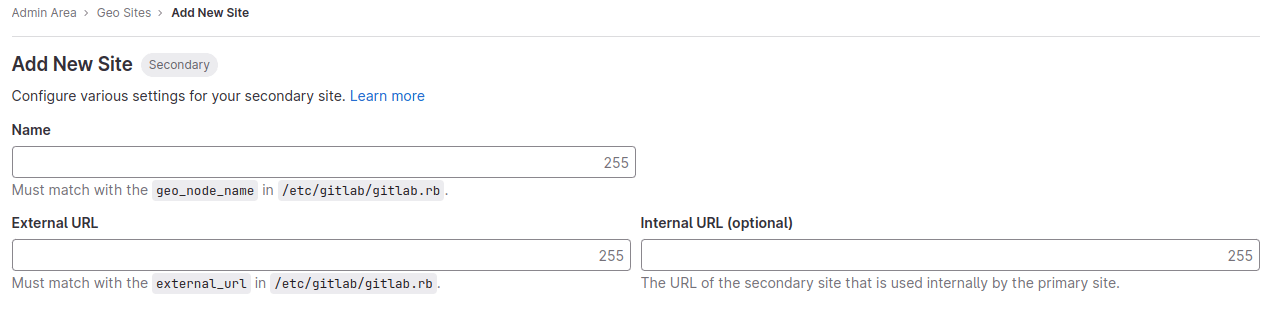
- In Name, enter the value for
gitlab_rails['geo_node_name']in/etc/gitlab/gitlab.rb. These values must always match exactly, character for character. - In External URL, enter the value for
external_urlin/etc/gitlab/gitlab.rb. These values must always match, but it doesn’t matter if one ends with a/and the other doesn’t. - Optional. In Internal URL (optional), enter an internal URL for the secondary site.
- Optional. Select which groups or storage shards should be replicated by the secondary site. Leave blank to replicate all. For more information, see selective synchronization.
- Select Save changes to add the secondary site.
-
SSH into each Rails, and Sidekiq node on your secondary site and restart the services:
gitlab-ctl restartCheck if there are any common issues with your Geo setup by running:
gitlab-rake gitlab:geo:checkIf any of the checks fail, check the troubleshooting documentation.
-
SSH into a Rails or Sidekiq server on your primary site and login as root to verify the secondary site is reachable or there are any common issues with your Geo setup:
gitlab-rake gitlab:geo:checkIf any of the checks fail, check the troubleshooting documentation.
After the secondary site is added to the Geo administration page and restarted, the site automatically starts replicating missing data from the primary site in a process known as backfill. Meanwhile, the primary site starts to notify each secondary site of any changes, so that the secondary site can act on those notifications immediately.
Be sure the secondary site is running and accessible. You can sign in to the secondary site with the same credentials as were used with the primary site.
Step 4. (Optional) Using custom certificates
You can safely skip this step if:
- Your primary site uses a public CA-issued HTTPS certificate.
- Your primary site only connects to external services with CA-issued (not self-signed) HTTPS certificates.
Custom or self-signed certificate for inbound connections
If your GitLab Geo primary site uses a custom or self-signed certificate to secure inbound HTTPS connections, this can be either a single-domain or multi-domain certificate.
Install the correct certificate based on your certificate type:
-
Multi-domain certificate that includes both primary and secondary site domains: Install the certificate at
/etc/gitlab/sslon all Rails, Sidekiq, and Gitaly nodes in the secondary site. -
Single-domain certificate where the certificates are specific to each Geo site domain: Generate a valid certificate for your secondary site’s domain and install it at
/etc/gitlab/sslfollowing these instructions on all Rails, Sidekiq, and Gitaly nodes in the secondary site.
Connecting to external services that use custom certificates
A copy of the self-signed certificate for the external service needs to be added to the trust store on all the primary site’s nodes that require access to the service.
For the secondary site to be able to access the same external services, these certificates must be added to the secondary site’s trust store.
If your primary site is using a custom or self-signed certificate for inbound HTTPS connections, the primary site’s certificate needs to be added to the secondary site’s trust store:
-
SSH into each Rails, Sidekiq, and Gitaly node on your secondary site and login as root:
sudo -i -
Copy the trusted certs from the primary site:
If you can access one of the nodes on your primary site serving SSH traffic using the root user:
scp root@<primary_site_node_fqdn>:/etc/gitlab/trusted-certs/* /etc/gitlab/trusted-certsIf you only have access through a user with sudo privileges:
# Run this from the node on your primary site: sudo tar --transform 's/.*\///g' -zcvf ~/geo-trusted-certs.tar.gz /etc/gitlab/trusted-certs/* # Run this on each node on your secondary site: scp <user_with_sudo>@<primary_site_node_fqdn>:geo-trusted-certs.tar.gz . tar zxvf ~/geo-trusted-certs.tar.gz -C /etc/gitlab/trusted-certs -
Reconfigure each updated Rails, Sidekiq, and Gitaly node in your secondary site:
sudo gitlab-ctl reconfigure
Step 5. Enable Git access over HTTP/HTTPS and SSH
Geo synchronizes repositories over HTTP/HTTPS, and therefore requires this clone method to be enabled. This is enabled by default, but if converting an existing site to Geo it should be checked:
On the primary site:
- On the left sidebar, at the bottom, select Admin.
- Select Settings > General.
- Expand Visibility and access controls.
- If using Git over SSH, then:
- Ensure “Enabled Git access protocols” is set to “Both SSH and HTTP(S)”.
- Follow the steps to configure fast lookup of authorized SSH keys in the database on all primary and secondary sites.
- If not using Git over SSH, then set “Enabled Git access protocols” to “Only HTTP(S)”.
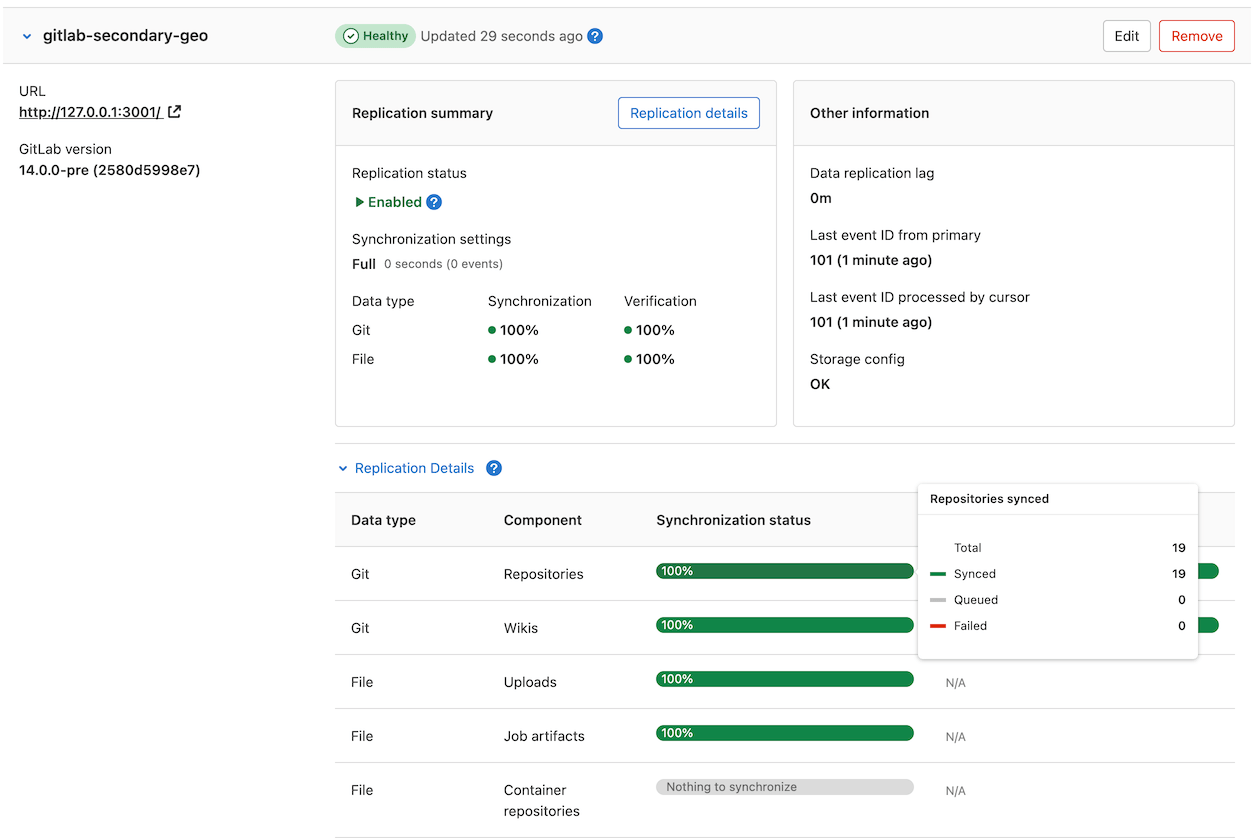
Step 6. Verify proper functioning of the secondary site
You can sign in to the secondary site with the same credentials you used with the primary site. After you sign in:
- On the left sidebar, at the bottom, select Admin.
- Select Geo > Sites.
- Verify that it’s correctly identified as a secondary Geo site, and that Geo is enabled.
The initial replication may take some time. The status of the site or the ‘backfill’ may still in progress. You can monitor the synchronization process on each Geo site from the primary site’s Geo Sites dashboard in your browser.
If your installation isn’t working properly, check the troubleshooting document.
The two most obvious issues that can become apparent in the dashboard are:
- Database replication not working well.
- Instance to instance notification not working. In that case, it can be
something of the following:
- You are using a custom certificate or custom CA (see the troubleshooting document).
- The instance is firewalled (check your firewall rules).
Disabling a secondary site stops the synchronization process.
If git_data_dirs is customized on the primary site for multiple
repository shards you must duplicate the same configuration on each secondary site.
Point your users to the Using a Geo Site guide.
Currently, this is what is synced:
- Git repositories.
- Wikis.
- LFS objects.
- Issues, merge requests, snippets, and comment attachments.
- Users, groups, and project avatars.
Troubleshooting
See the troubleshooting document.